Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Malware Analysis: Steps & Examples - CrowdStrike

Mastering Malware Analysis

Malware analysis lockysample.bin.zip Malicious activity

Feature Extraction and Detection of Malwares Using Machine Learning
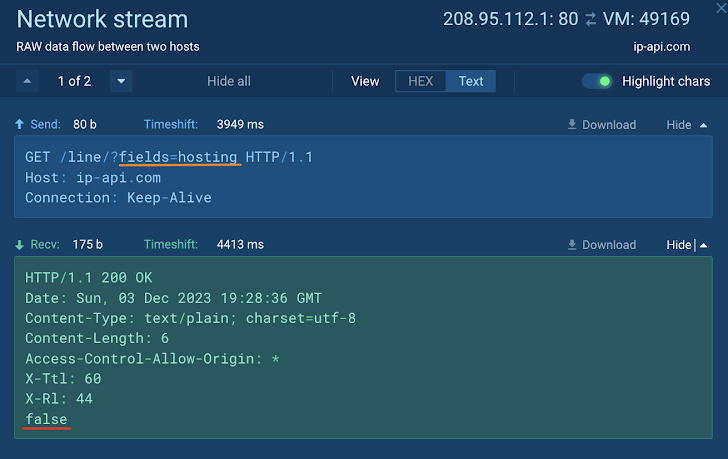
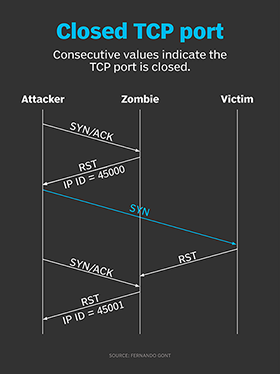
How to Analyze Malware's Network Traffic in A Sandbox

MetaDefender Cloud Advanced threat prevention and detection
Website Security Checker, Malware Scan

Malware analysis tt.7z Malicious activity
Malware analysis Malicious activity
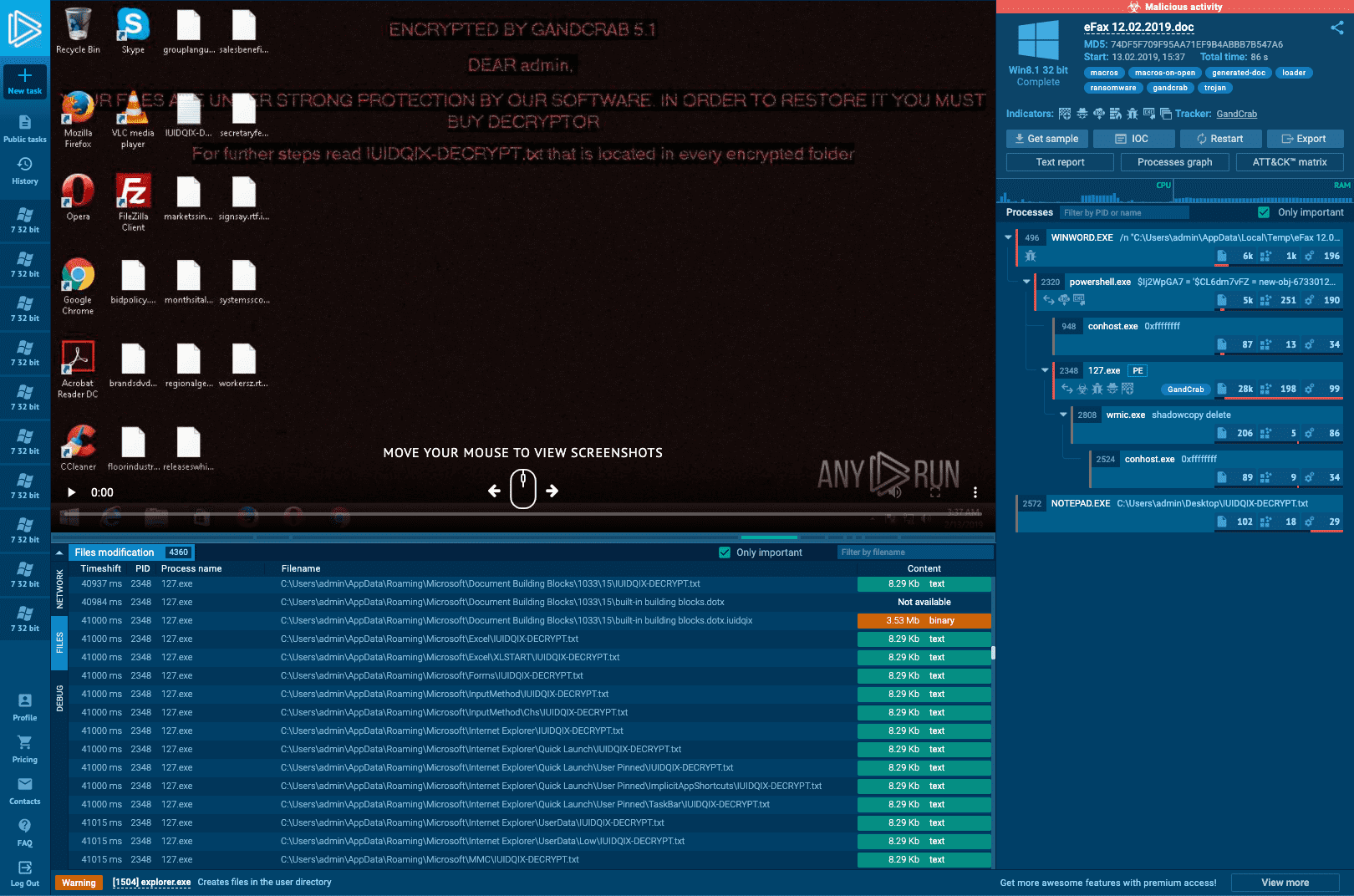
Interactive Online Malware Sandbox

An Elastic approach to large-scale dynamic malware analysis — Elastic Security Labs

Complex 'NKAbuse' Malware Uses Blockchain to Hide on Linux, IoT Machines
de
por adulto (o preço varia de acordo com o tamanho do grupo)