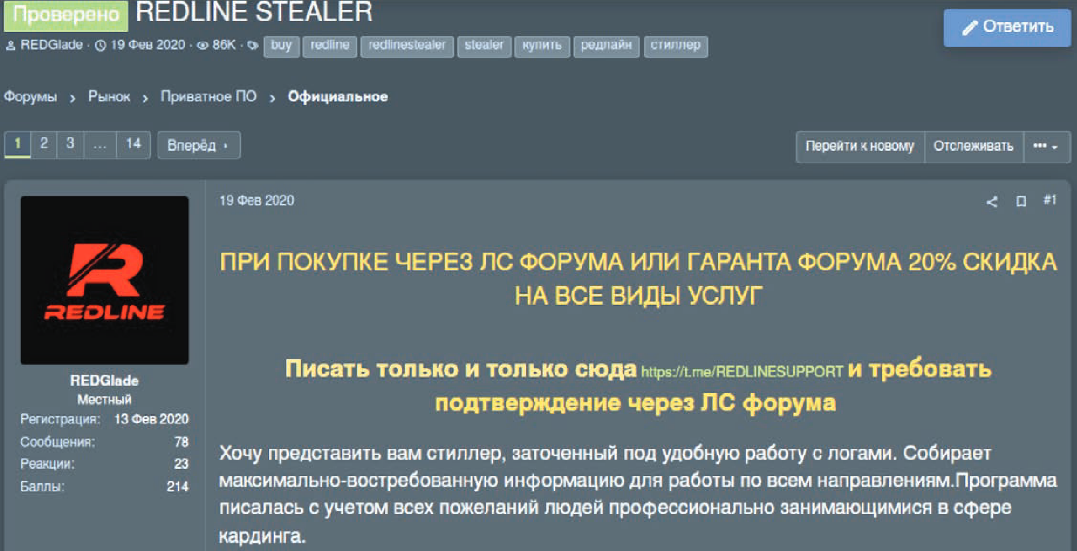
Do Not Cross The 'RedLine' Stealer: Detections and Analysis
Por um escritor misterioso
Descrição
The Splunk Threat Research Team provides a deep dive analysis of the RedLine Stealer threat and shares valuable insights to help enable blue teamers to defend against and detect this malware variant.

eSentire eSentire Threat Intelligence Malware Analysis: Redline…

Security Researchers Disrupt RedLine Stealer Operations!

eSentire eSentire Threat Intelligence Malware Analysis: Redline…
From ChatGPT to RedLine Stealer: The Dark Side of OpenAI and Google Bard - Veriti

Cyble — Redline Stealer being Distributed via Fake Express VPN Sites
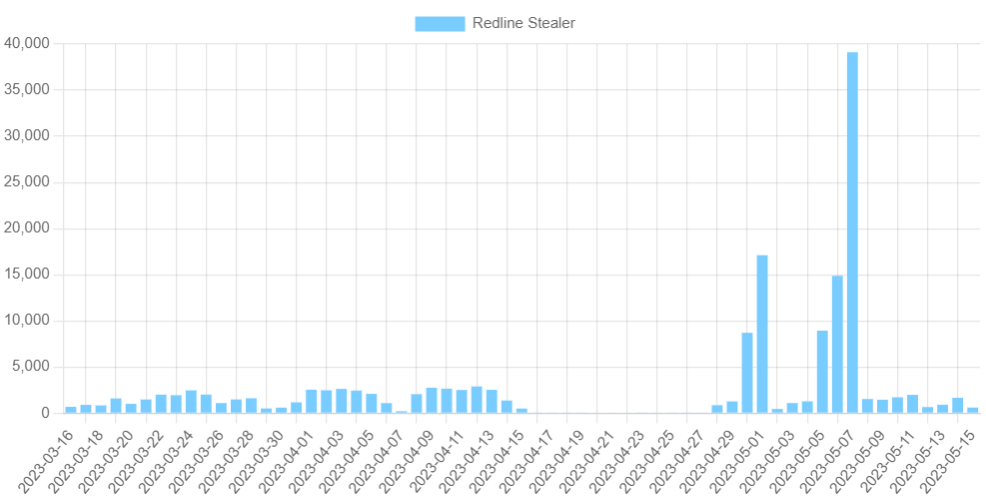
RedLine Stealer Issues 100,000 Samples - What is Happening? –
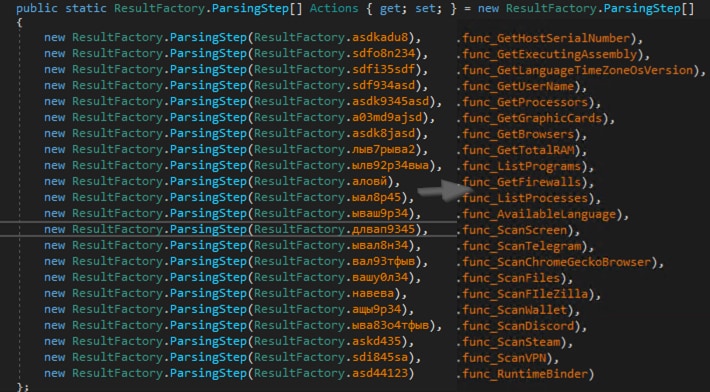
Do Not Cross The 'RedLine' Stealer: Detections and Analysis
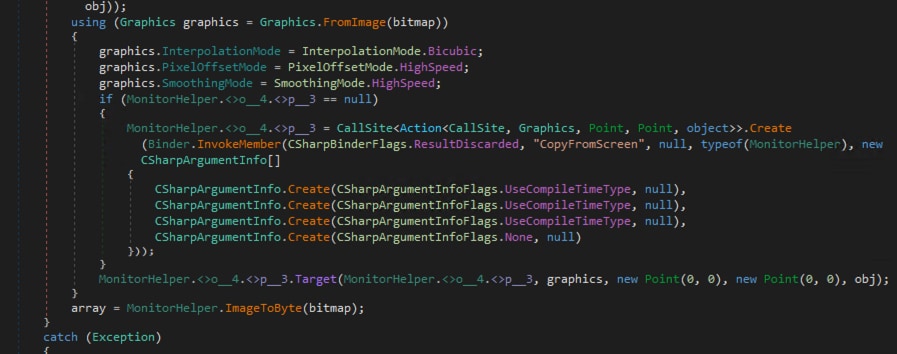
Do Not Cross The 'RedLine' Stealer: Detections and Analysis
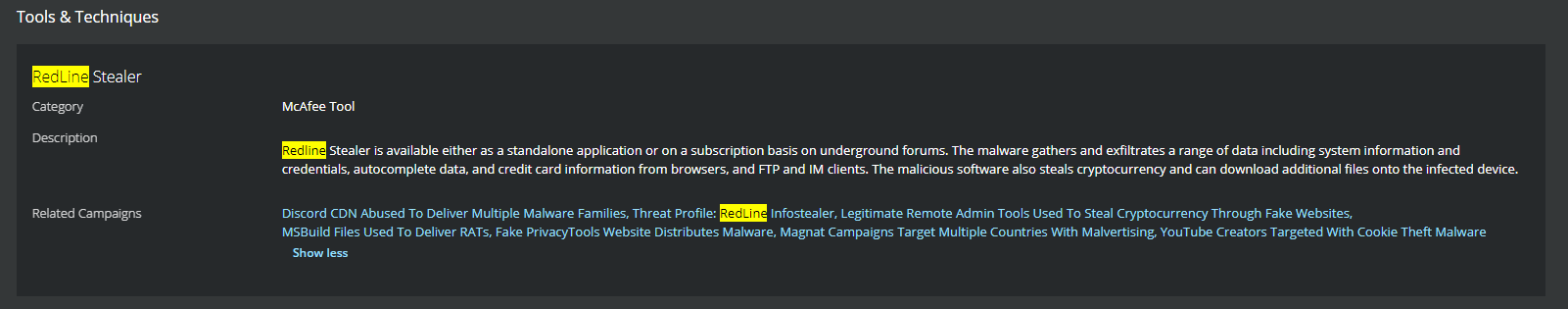
Trellix Global Defenders: Invasion of the Information Snatchers - Protecting against RedLine Infostealer
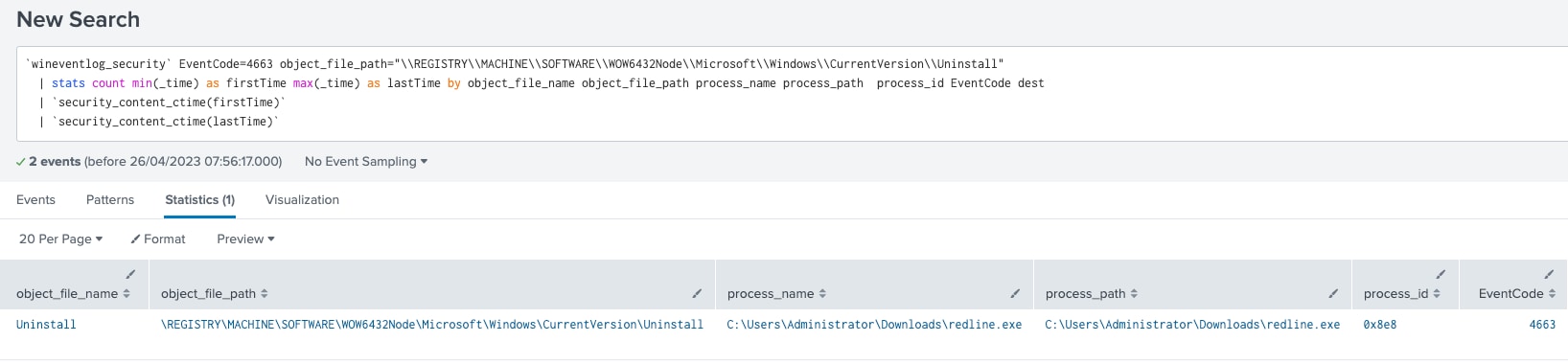
Do Not Cross The 'RedLine' Stealer: Detections and Analysis

Redline Stealer/Amadey Bot - Static Analysis and C2 Extraction
RedLine Stealer malware responsible for stealing majority of the credentials
de
por adulto (o preço varia de acordo com o tamanho do grupo)